This document gives an overview of the automatic and manual components provided by OWASP Zed Attack Proxy (ZAP) that are recommended for testing each of the OWASP Top Ten Project 2021 risks.
For the previous Top Ten see ZAPping the OWASP Top 10 (2017)
Note that the OWASP Top Ten Project risks cover a wide range of underlying vulnerabilities, some of which are not really possible to test for in a completely automated way. If a completely automated tool claims to protect you against the full OWASP Top Ten then you can be sure they are being ‘economical with the truth’!
The component links take you to the relevant places in an online version of the ZAP User Guide from which you can learn more.
Common Components |
The ‘common components’ can be used for pretty much everything, so can be used to help detect all of the Top 10 | |
| Manual | Manipulator-in-the-middle proxy | |
| Manual | Manual request / resend | |
| Manual | Scripts | |
| Manual | Community Scripts | |
| Manual | Search | |
A1 Broken Access Control |
||
| Automated | Scan Rules tagged with: OWASP_2021_A01 | |
| Automated | Access Control Testing* | |
| Manual | Port Scanner* | |
| Manual | Wappalyzer - Technology detection* | |
A2 Cryptographic Failures |
||
| Automated | Scan Rules tagged with: OWASP_2021_A02 | |
A3 Injection |
||
| Automated | Scan Rules tagged with: OWASP_2021_A03 | |
| Manual | Fuzzer, combined with the FuzzDb* and SVN Digger* files | |
| Manual | Eval Villain | |
A4 Insecure Design |
||
| Automated | Scan Rules tagged with: OWASP_2021_A04 | |
A5 Security Misconfiguration |
||
| Automated | Scan Rules tagged with: OWASP_2021_A05 | |
| Manual | Spider | |
| Manual | Ajax Spider | |
| Manual | Session comparison | |
| Manual | Access Control Testing* | |
A6 Vulnerable and Outdated Components |
||
| Automated | Scan Rules tagged with: OWASP_2021_A06 | |
| Manual | Wappalyzer - Technology detection* | |
A7 Identification and Authentication Failure |
||
| Manual | HTTP Sessions | |
| Manual | Spider | |
| Manual | Forced Browse | |
| Manual | Token Generator* | |
| Automated | Access Control Testing* | |
A8 Software and Data Integrity Failures |
||
| Automated | Scan Rules tagged with: OWASP_2021_A08 | |
A9 Security Logging and Monitoring Failures |
||
| Automated / Manual | The Spider(s), Active Scanner, Fuzzer, and Access Control addon can all be used to generate traffic and “attacks” which are potential sources/causes for logging and alerting. | |
A10 Server-Side Request Forgery |
||
| Automated | OAST Support | |
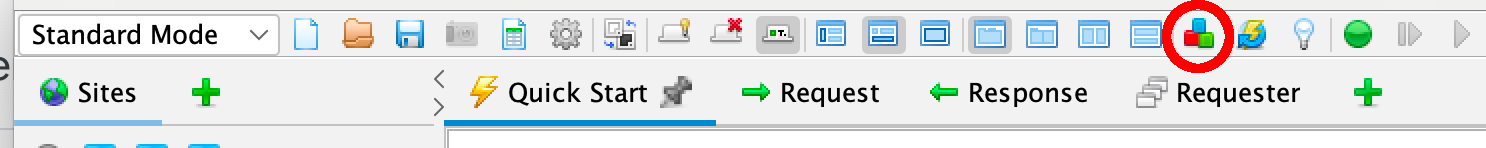
* The stared add-ons (and Beta and Alpha scan rules) are not included by default in the full ZAP release but can be downloaded from the ZAP Marketplace via the ‘Manage add-ons’ button on the ZAP main toolbar.